In September 2024, Bangladesh Cyber Security Intelligence (BCSI) published a detailed analytical report on the India-linked advanced persistent threat (APT) group known as SloppyLemming, documenting its targeting of Bangladeshi government institutions and law enforcement agencies. At that time, BCSI highlighted the group’s use of credential harvesting portals, Cloudflare Workers-based phishing infrastructure, and remote access implants designed to collect sensitive government information.
SloppyLemming, also tracked by multiple international cybersecurity firms under aliases such as Outrider Tiger and Fishing Elephant, has been active across South Asia since at least 2021. Beyond Bangladesh, the group has previously been linked to targeting efforts in Pakistan, Sri Lanka, and China, focusing primarily on government ministries, defense-related organizations, energy providers, telecommunications operators, and strategic research institutions. The targeting pattern consistently indicated intelligence-driven objectives aligned with long-term regional monitoring rather than financially motivated cybercrime.
Recent international reporting has now revealed that the same threat actor conducted a sustained cyber-espionage campaign between January 2025 and January 2026, specifically targeting government and critical infrastructure entities in Pakistan and Bangladesh. The campaign reportedly involved a multi-stage infection chain, encrypted in-memory implants, and cloud-hosted command-and-control infrastructure marking a technical escalation compared to earlier observed operations.
The resurgence of activity demonstrates that SloppyLemming has not only remained active but has further refined and evolved its operational techniques. The transition from primarily credential-harvesting campaigns to more advanced fileless malware deployment suggests increased operational maturity, improved evasion capability, and a structured espionage objective within the South Asian geopolitical landscape.
Taken together, these developments reinforce earlier BCSI assessments that SloppyLemming represents a persistent and adaptive regional threat actor with sustained interest in government and strategic infrastructure within Bangladesh and neighboring countries.
Background: Previous BCSI Warning
BCSI previously documented SloppyLemming’s use of:
- Cloudflare Workers-based phishing infrastructure
- Credential harvesting portals
- Remote access payloads
- Exploitation of legacy software vulnerabilities
At that time, the targeting pattern indicated intelligence-focused objectives across South Asia.
The latest campaign demonstrates a shift toward more advanced malware delivery and stealth execution techniques.
Recent Campaign Overview (2025–2026)
According to newly published research, the group deployed a multi-stage infection chain involving:
- Spear-phishing emails with malicious PDF lures
- Abuse of Microsoft ClickOnce deployment technology
- DLL side-loading via legitimate binaries
- Encrypted in-memory implants
- Cloud-hosted command-and-control infrastructure
The campaign primarily targeted:
- Government agencies
- Regulatory authorities
- Law enforcement bodies
- Energy and telecommunications sectors
The structured targeting pattern suggests continued intelligence collection objectives.
Technical Attack Flow
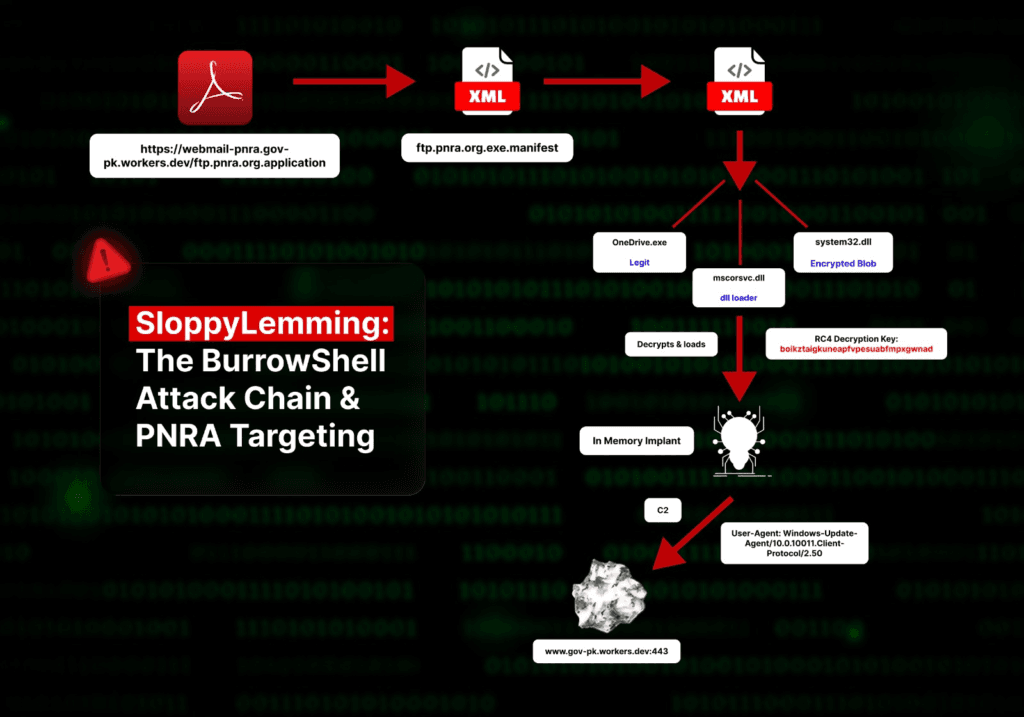
As illustrated in the diagram below (based on research published by Arctic Wolf Labs), the SloppyLemming campaign follows a structured multi-stage infection chain.
The attack begins with a spear-phishing lure that redirects the victim to a Cloudflare Workers-hosted domain impersonating a legitimate government service. A malicious ClickOnce application is then downloaded, which retrieves an XML manifest file and initiates staged payload execution.
The deployment leverages DLL side-loading, where a legitimate Microsoft-signed binary loads a malicious DLL. This DLL decrypts an encrypted payload and executes the final implant directly in memory, avoiding disk-based detection.
The backdoor establishes encrypted HTTPS communication with cloud-hosted command-and-control infrastructure. Notably, the traffic is disguised to resemble legitimate Windows Update activity, enabling the malware to blend into normal network behavior.
This multi-layered delivery mechanism reflects a deliberate effort to maximize stealth, persistence, and evasion.
Operational Evolution
Compared to the earlier campaigns previously reported by BCSI, the latest activity attributed to SloppyLemming reflects a clear advancement in operational maturity. The group has significantly improved the sophistication of its payload delivery mechanisms, moving beyond simple credential harvesting toward structured, multi-stage malware deployment chains.
The campaign demonstrates the use of encrypted, in-memory implant execution, allowing malicious payloads to operate without being written to disk. This fileless approach reduces forensic visibility and increases the likelihood of bypassing traditional endpoint defenses. Additionally, the threat actor has expanded its reliance on cloud-hosted infrastructure, particularly leveraging edge services to host and rotate command-and-control endpoints. This tactic enables malicious traffic to blend into legitimate cloud service activity, complicating detection and blocking efforts.
Another notable evolution is the improved evasion strategy through impersonation of trusted services, including Windows Update-like traffic patterns and legitimate application deployment mechanisms. These enhancements indicate a more structured and disciplined espionage capability compared to earlier observed activity.